Issue channel access token v2.1
There are four types of channel access tokens available on the LINE Platform. Of these, channel access tokens v2.1 and stateless channel access tokens can be generated using JSON Web Token (JWT).
This page explains how to specify an assertion signing key, how to generate a JWT from a signing key, and how to issue a channel access token using the generated JWT, targeting channel access tokens v2.1.
Process of issuing a channel access token v2.1
The process of issuing a channel access token v2.1 is illustrated in the diagram below. This diagram shows the following three steps:
- Create an assertion signing key (Step 1 in the diagram)
- Generate a JWT (Step 6 in the diagram)
- Issue a channel access token v2.1 (Step 7 in the diagram)
The authentication method for issuing a channel access token v2.1 is in accordance with Using JWTs as Authorization Grants (RFC 7523). This is the Assertion Framework of OAuth Assertion Framework (RFC 7521) using JSON Web Token (RFC 7519).
Create an assertion signing key
Issuing an assertion signing key is done in the these two steps:
1. Generate a key pair for the assertion signing key
To create a JWT, you must first create an assertion signing key pair (private key, public key).
Assertion signing key specification
You can use a JSON Web Key (RFC7517) that meets these criteria as an assertion signing key for JWT.
- The key must be an RSA public key. (Set the
ktyproperty toRSA) - The RSA key must be 2048 bits long.
- Use RS256 (RSASSA-PKCS1-v1_5 with SHA256) as the signing algorithm. (Set the
algproperty toRS256) - State that the public key is for signing. (Set
useorkey_opsas instructed in the table below).
Therefore, the public key of the assertion signing key must contain these properties:
| Property | Description |
|---|---|
kty | Cryptographic algorithm family used in key. Set to RSA. |
alg | Algorithm used in the key. Set to RS256. |
use*1 | Usage of the key. Set to sig. |
key_ops*1 | Operation for the key to be used. Set to ["verify"] only. |
e | Absolute value for restoring public key |
n | Cryptographic index for restoring public key |
*1 Specify either one of use or key_ops.
Make sure the public key you register doesn't have the kid property. An error occurs if the public key of the assertion signing key has the kid property. This is because that kid is issued only when you register a public key in the LINE Developers Console.
You can choose to write your own program to generate an assertion signing key pair based on the published specification, but you can use libraries that meet the specification to generate a key more easily.
Here is an example of the steps for generating an assertion signing key:
- Create a key pair with jwx (Go language library)
- Create a key pair with JWCrypto (Python library)
- Create a key pair with a browser
Create a key pair with jwx (Go language library)
You can generate a key pair with the jwx command line tool. The command line tool is part of jwx, an open source Go language library, used for JWT implementation. If you don't have Go language development environment set up, download Go from the Go language official site.
To issue an assertion signing key:
1. Install the jwx command line tool
Install the jwx command line tool with this command.
When the installation is complete, you'll see the path where the jwx command line tool has been installed.
You should configure the path so that the commands in subsequent steps can be executed.
2. Generate private key and public key
Create a private key with this command.
Create a public key with the private key.
If successful, a private key and public key are generated:
Private key example
Public key example
Create a key pair with JWCrypto (Python library)
You can create a key pair with an open source Python library, JWCrypto for JWT implementation. To use JWCrypto, you need Python 3 and pip installed on your computer. If you don't have Python 3, download an installer for your OS from the Python official site and proceed with installation. Pip is installed when Python3 is installed. If you have Python 3 but no pip, see the pip documentation for installation.
To issue an assertion signing key:
1. Install JWCrypto
Install JWCrypto with this command.
2. Write code to create private and public keys
Create a python file that generates private and public keys by specifying kty as RSA, alg as RS256, use as sig, and size as 2048, like below.
Save the python file using any file name you want. In this case, the file name is app.py.
In the same directory where you saved the python file, generate a public key based on the private key with this command.
If successful, a private key and public key are generated in the standard output:
Private key example
Public key example
Generate a key pair with a browser
If your browser supports Web Crypto API, you can use the SubtleCrypto.generateKey() method to generate a private key and public key. If you have Google Chrome, enter and run this code from the console of Chrome's developer tools.
If successful, a private key and public key are generated.
Private key example
Public key example
2. Register public key and get kid
After you generate a key pair, register the public key in the LINE Developers Console and in return, get kid. To register your public key, visit the console and open the channel settings for your channel. Click the Basic settings tab and then the Register a public key button next to assertion signing key. Enter the public key and finalize the registration with the Register button.
If the public key is successfully registered, you'll get kid in return.
Generate a JWT
JWT is a string and contains header, payload, and signature, all of which are required. To generate a JWT, you can use any JWT library or write your own code from scratch with your assertion signing key.
Header
The header must contain these properties:
| Property | Type | Description |
|---|---|---|
alg | String | The algorithm for JWT generation. Set the value to "RS256" |
typ | String | The type of the token. Set the value to "JWT". |
kid | String | The key ID. Set the value to the kid property returned for 2. Register public key and get kid. |
This is an example of a decoded header:
Payload
The payload must contain these properties:
| Property | Type | Description |
|---|---|---|
iss | String | Channel ID. You can retrieve your channel ID from the LINE Developers Console. The value of this property and sub must be the same. |
sub | String | Channel ID. You can retrieve your channel ID from the LINE Developers Console. The value of this property and iss must be the same. |
aud | String | Set the value to https://api.line.me/. |
exp | Number | The expiration time of the JWT in UNIX time (in seconds). The maximum lifetime of a JWT assertion is 30 minutes. |
token_exp | Number | The channel access token's validity period in seconds. The maximum lifetime of a channel access token is 30 days. |
This is an example of a decoded payload:
Signature
You need to sign the header and payload to generate a JWT. Learn how to create a signature and use the result to generate a JWT with node-jose (Node.js library) or PyJWT (Python library).
Generate a JWT with node-jose (Node.js library)
To create a signature and generate a JWT with node-jose, a Node.js library, make sure you have Node.js and node-jose installed.
The example code below uses node-jose to sign with a private key to generate a JWT. To generate your own JWT using this code, first change the value of privateKey to the private key of your assertion signing key. Also change header and payload to your own values and run the code. Make sure to sign with your private key to prove that the content isn't tampered with. See node-jose for more information on the usage.
Sign the Base64url-encoded header, Base64url-encoded claim set, and a private key (such as an rsa_private.pem file), using the algorithm you specified in the header. The Base64url-encoded result is your JWT. Here is an example of JWT.
Generate a JWT with PyJWT (Python library)
To create a signature and generate a JWT with PyJWT, you need Python and PyJWT installed.
The example code below uses PyJWT to sign with a private key to generate a JWT. To generate your own JWT using this code, first change the value of privateKey to the private key of your assertion signing key. Also, change kid in headers and payload to your own values and run the code. Make sure to sign with your private key to prove that the content isn't tampered with. See PyJWT for more information on the usage.
Sign the Base64url-encoded header, Base64url-encoded claim set, and a private key using the algorithm you specified in the header. The Base64url-encoded result is your JWT. Here is an example of JWT.
Issue a channel access token v2.1
You can issue a channel access token v2.1 with the JWT assertion you generated.
- When you request for a channel access token v2.1, the response you get is a pair of the channel access token and a unique key ID (
key_id). For proper management of channel access tokens, safely store the channel access token and key ID pair. - The key ID is an identifier added to the Messaging API on June 22, 2020. If your app uses a channel access token v2.1 without a key ID, we recommend that you re-issue a channel access token v2.1 and safely store the token and key ID pair. If you re-issue a channel access token, make sure to update your bot to use the new token.
The process for getting a channel access token v2.1 is as follows:
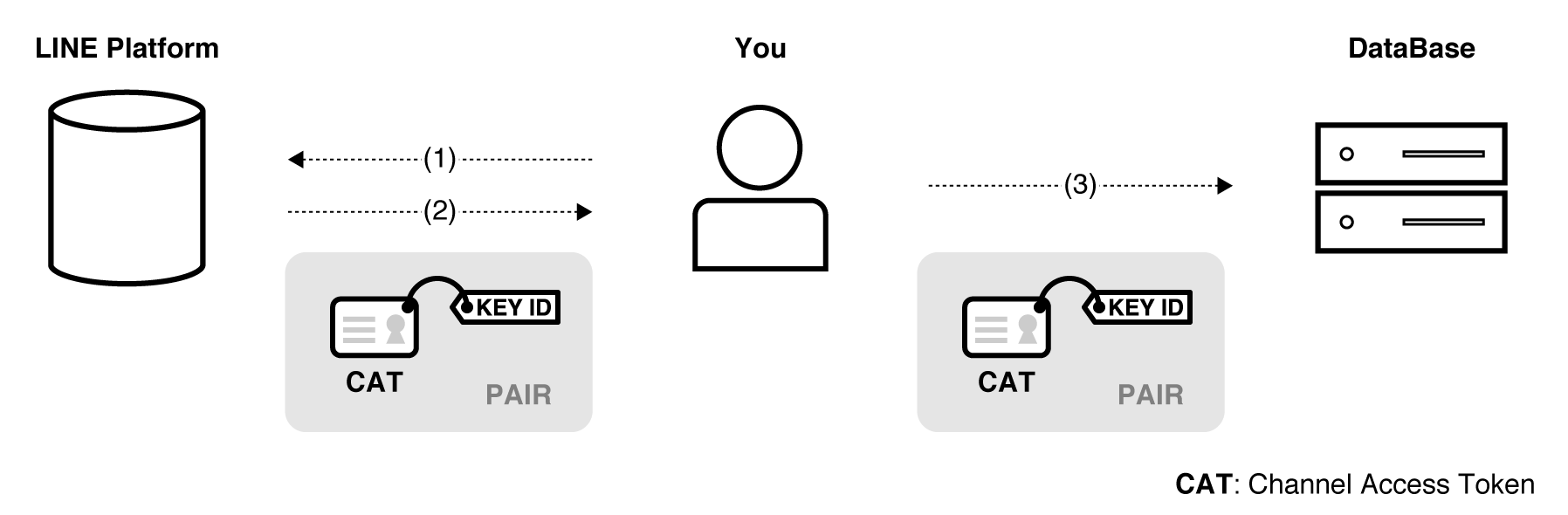
- Execute the Issue channel access token v2.1 endpoint with the JWT you generated to issue a channel access token.
- The LINE Platform sends you a channel access token and a key ID.
- Store the channel access token and key ID pair in a database or somewhere else.
Revoke channel access token v2.1
You can revoke a channel access token v2.1 if your channel access token is valid.
You can use an invalid channel access token to execute the Revoke channel access token v2.1 endpoint and get no error. You can get key IDs for valid channel access tokens using the Get all valid channel access token key IDs v2.1 endpoint. You can identify valid access tokens by matching the obtained key IDs with pairs of a channel access token and a key ID stored in a database, etc.
The process for revoking a channel access token v2.1 is as follows:
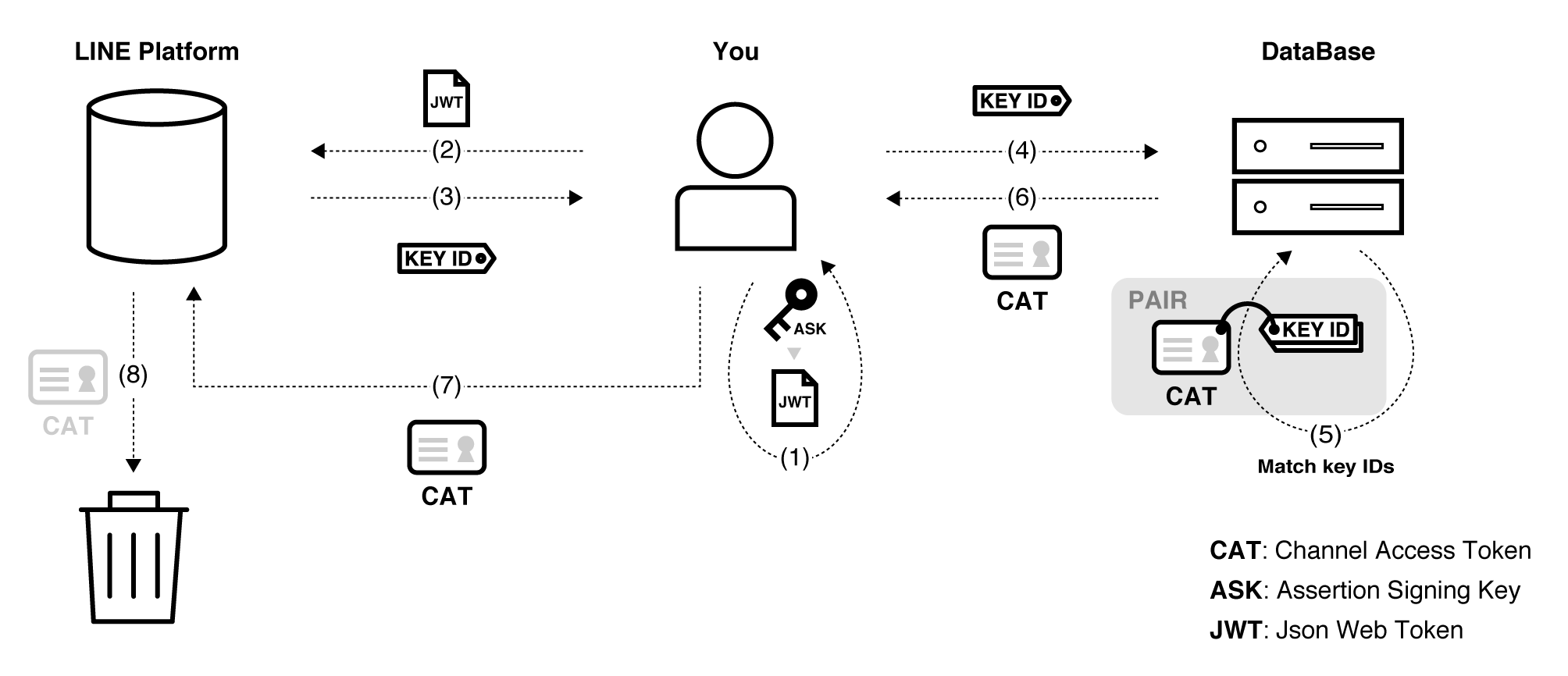
- Re-generate a JWT from the assertion signing key you stored.
- Execute the Get all valid channel access token key IDs v2.1 endpoint with the JWT.
- The LINE Platform returns key IDs for valid channel access tokens.
- Check the key IDs against your database.
- See if you have a channel access token and key ID pair that matches any of the key IDs returned.
- Retrieve the channel access token validated.
- Execute the Revoke channel access token v2.1 endpoint with the channel access token.
- The LINE Platform revokes the channel access token.


